Cybersecurity is a set of measures to safeguard electronic devices, information they store, and networks from digital threats. Cybersecurity research topics are essential for investigating and tackling these ever-evolving threats. According to an FBI report, the Internet Crime Complaint Center registered 880,418 complaints from victims in 2023, a 10% increase compared to 2022. These include appeals regarding viruses, malware, phishing attacks, ransomware, and other types of cyberattacks.
This collection, compiled by Custom-Writing.org experts, offers excellent cyber security topics for presentation and research. Additionally, you will find brief overviews of current trends and tips on how to choose a topic and write a winning information security research paper.
- 🔝 Top 10 Topics
- ✅ Current Trends
- ⭐ Top 10 Cybersecurity Topics
- 🔒 Computer Security Topics
- 🎓 Research Paper Topics
- 👨💻 Thesis Topics
- 💽 Topics for Presentation
- ❓ Research Questions
- 💡 Debate Topics
- ✨ Interesting Topics
- 💾 Operational Security Topics
- 📡 Mobile Cybersecurity Topics
- 🤔 How to Choose a Topic
- ✍️ Writing Tips
- 🔍 References
🔝 Top 10 Cyber Security Research Topics
- How does malware work?
- The principle of zero trust access
- 3 phases of application security
- Should removable media be encrypted?
- The importance of network security
- The importance of end-user education
- Cloud security posture management
- Do biometrics ensure security of iPhone?
- Can strong passwords protect information?
- Is security in critical infrastructure important?
✅ Current Cybersecurity Trends
Cybersecurity is a rapidly evolving field. Tech innovations and massive digital adoption drive criminal activities and protective measures forward. Here are the hottest trends that will likely be shaping the field of cybersecurity research in the near future.
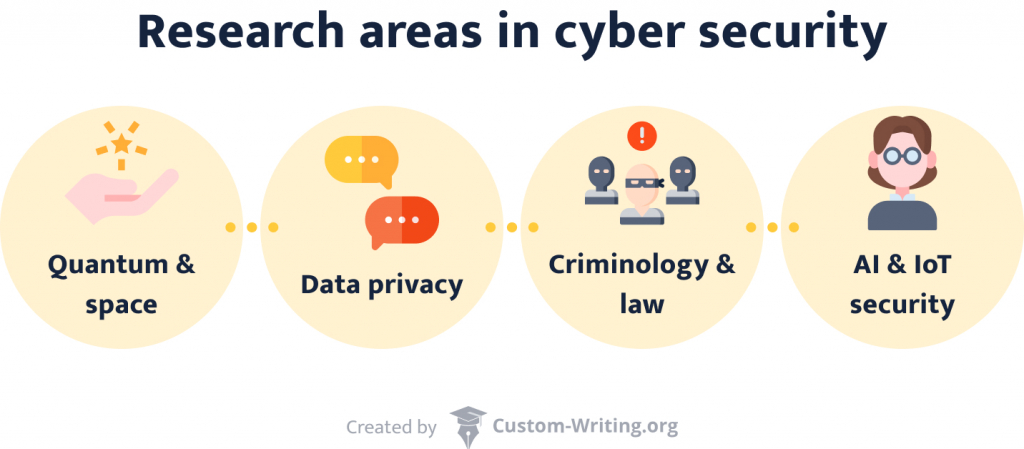
- Cloud-based cybersecurity. Thanks to their scalability and flexibility, cloud computing solutions are the new normal in the digital business world. These benefits contribute to the rising popularity of cloud-based cybersecurity shields, which also offer cost-effectiveness amid the rising need for data protection.
- IoT implementation and protection. Internet of Things (IoT) systems are widely adopted in various settings, from smart homes to IoT-powered industrial facilities. However, the compound nature of IoT architecture often deprives it of a comprehensive security layer and makes it a frequent target of hacker attacks. Innovative IoT security protocols will be increasingly needed in the coming years, which will lead to the greater use of IoT tech in all domains of human activity.
- AI use in cybersecurity solutions. AI is a next-gen technology with many use cases, including real-time anomaly and threat detection and cyberattack prevention. Machine learning is an assistive tool that helps AI algorithms become more sophisticated and increase their predictive power.
- Data privacy and compliance. GDPR in the EU and CCPA in California are only a couple of examples of overarching data privacy regulations that digital businesses must comply with. Knowing these laws and regulations, as well as investing in compliance reporting and monitoring, is essential for legal businesses.
- Zero trust architecture as an innovative solution. The zero-trust model of cybersecurity is the new golden standard. It introduces robust user verification tools at all levels to prevent attacks from any source.
These trends will likely define the cybersecurity landscape for years to come. Keeping pace with innovations in these areas is key to your grasp of the present-day cybersecurity industry.
⭐ Top 10 Cybersecurity Topics 2026
- Ways of detecting and responding to cyber attacks
- Social media’s role in cybersecurity
- Impact of cloud computing on security protocols
- Internet of things and its implications for security
- The effectiveness of existing protocols
- Emerging threats and ways to stay ahead of them
- Approaches to developing more effective cybersecurity policies
- Ethical implications of cybersecurity practices
- The development of quantum-safe cryptography
- The challenges of securing virtual environments from identity theft
🔒 Computer Security Topics to Research
Safe computer and network usage is crucial. It concerns not only business but also individuals. Security programs and systems ensure this protection. Explore them with one of our topics:
- How do companies avoid sending out confidential information? Sending an email to the wrong person has happened to the best of us. But what happens if the message’s contents were classified? For your paper, you can find out what technologies can prevent such slip-ups.
- What are the best ways to detect malicious activity? Any organization’s website gets plenty of daily traffic. People log in, browse, and interact with each other. Among all of them, it might be easy for an intruder to slip in.
- Internet censorship: classified information leaks. China takes internet censorship to the next level. Its comprehensive protection policies gave the system the nickname Great Firewall of China. Discuss this technology in your essay.
- Encrypted viruses as the plague of the century. Antivirus programs are installed on almost every computer. They prevent malicious code from tampering with your data. In your paper, you can conduct a comparison of several such programs.
- What are the pros and cons of various cryptographic methods? Data privacy is becoming more and more critical. That’s why leading messaging services frequently advertise with their encryption technologies.
- What makes blockchain secure? This technique allows anonymity and decentralization when working with cryptocurrencies. How does it work? What risks are associated with it?
- What are the advantages of SIEM? Security Incident and Event Management helps organizations detect and handle security threats. Your essay can focus on its relevance for businesses.
- What are the signs of phishing attempts?
- Discuss unified cyber security standards in healthcare.
- Compare and contrast various forms of data extraction techniques.
- What do computers need protocols for?
- Debate the significance of frequent system updates for data security.
- What methods does HTTPS use that make it more secure than HTTP?
- The role of prime numbers in cryptography.
- What are public key certificates, and why are they useful?
- What does a VPN do?
- Are wireless internet connections less secure than LAN ones? If so, why?
- How do authentication processes work?
- What can you do with IP addresses?
- Explain the technology of unlocking your phone via facial recognition vs. your fingerprint.
- How do you prevent intrusion attempts in networks?
- What makes Telnet vulnerable?
- What are the phases of a Trojan horse attack?
- Compare the encryption technologies of various social networks.
- Asymmetric vs. symmetric algorithms.
- How can a person reach maximum security in the computer networking world?
- Discuss autoencoders and reveal how they work.
🎓 Cyber Security Research Paper Topics
- The impact of quantum technologies on cybersecurity. Analyze how the development of quantum technologies could affect the cybersecurity industry. Investigate the possible risks and opportunities.
- Cybersecurity evolution: trends shaping our digital future. In your research paper, discuss the latest trends in the cybersecurity field. Focus on their potential impact on individuals, organizations, and society.
- The security vulnerabilities of IoT. Investigate common security flaws in IoT devices and potential attack vectors. Consider the consequences of using weak passwords and insecure communication protocols.
- Humans and AI as partners in cyber defense. Dwell on the future of human-AI partnership in cybersecurity and the skills required for this collaboration. Discuss potential discrimination risks in AI-driven security systems.
- Personal consequences of cyberattacks. Research how cyberattacks can affect people. Consequences can include financial loss to identity theft and even physical harm. We recommend selecting a specific attack type and clarifying its personal consequences.
- The most effective countermeasures against cyberattacks.
- Network traffic analysis and its role in cyber security.
- Basic procedures for computer forensics and investigations.
- The effectiveness of international cooperation in combating cyber threats.
- Cybersecurity in the field of public administration.
- The nature and dangers of cyber terrorism.
- Anti-phishing technologies and their role in email security.
- The use of machine learning to detect and prevent cyberattacks.
- Ways of optimizing cyber risk management by addressing human vulnerabilities.
- The role of cybersecurity in ensuring industrial safety.
- Wireless hacking techniques and possible ways to counter them.
- The role of blockchain in future wireless mobile networks
Cybercrime Topics for a Research Paper
Knowledge is one of today’s most valuable assets. Because of this, cybercrimes usually target the extraction of information. This practice can have devastating effects. Do you want to learn more about the virtual world’s dark side? This section is for you.
- Give an overview of the various types of cybercrimes today. Cybercriminals are becoming more and more inventive. It’s not easy to keep up with the new threats appearing every day. What threats are currently the most prominent?
- How does cryptojacking work, and why is it problematic? Cryptocurrency’s value explosion has made people greedy. Countries such as Iceland have become a haven for datamining. Explore these issues in your essay.
- Analyze the success rate of email frauds. You’ve probably seen irrelevant ads in your spam folder before. They often sound so silly it’s hard to believe they work. Yet, unfortunately, many people become victims of such scams.
- How did the WannaCry malware work? WannaCry was ransomware that caused global trouble in 2017. It led to financial losses in the billions. What made it so dangerous and hard to stop?
- Give famous examples of cybercrimes that targeted people instead of money. Not all cybercrimes want to generate profit. Sometimes, the reasons are political or personal. Explore several instances of such crimes in your essay. How did they pan out?

- Analyze the implications of the Cyberpunk 2077 leak. The game’s bugs and issues made many people angry. Shortly after its flop, hackers released developer CD Projekt Red’s source codes. What far-reaching consequences could this have?
- Why do hackers commit identity theft? Social media has made it easy to steal identities. Many like to display their lives online. In your paper, research what happens to the victims of identity thefts.
- Should governments punish cybercrimes like real-life crimes?
- How does ransomware work?
- Describe the phases of a DDoS attack.
- What cybercrime cases led to changes in the legislature?
- Track the evolution of online scams.
- Online grooming: how to protect children from predators.
- Are cybercrimes “gateway crimes” that lead to real-life misbehavior?
- What are man-in-the-middle attacks?
- Big data and the rise of internet crimes.
- Are cybercrimes more dangerous to society than they are to corporations?
- Is the internet increasing the likelihood of adolescents engaging in illegal activities?
- Do the downsides of cyberlife outweigh its positives?
- Is constantly checking your crush’s Facebook page cyberstalking?
- How do you recognize your online date is a scam?
- Describe what happens during a Brute Force attack.
- What’s the difference between pharming and phishing?
- The Lehman Bank cybercrimes.
- Should the punishments for cybercriminals be harsher than they are now?
- Compare various types of fraud methods.
- How do you mitigate a denial-of-service attack?
Topics for a Research Paper on Hacking
Blinking screens and flashing lines of code: the movie industry makes hacking look fascinating. But what actually happens when someone breaks into another person’s computer’s system? Write a paper about it and find out! The following prompts allow you to dive deeper into the subject.
- Is it vital to keep shutting down online movie streaming sites? Many websites offer free movie streaming. If one of their domains gets closed down, they just open another one. Are they a threat to the industry that must be stopped? Or should cyber law enforcement rather focus on more serious crimes?
- Explore the ethical side of whistleblowing. WikiLeaks is a platform for whistleblowers. Its founder, Julian Assange, has been under arrest for a long time. Should whistleblowing be a crime? Why or why not?
- How did Kevin Mitnick’s actions contribute to the American cyber legislature? Mitnick was one of the US’s first most notorious hackers. He claimed to have broken into NORAD’s system. What were the consequences?
- Examine how GhostNet operates. GhostNet is a large organization attacking governments. Its discovery in 2009 led to a major scandal.
- Describe how an SQL injection attack unfolds. Injection attacks target SQL databases and libraries. This way, hackers gain unauthorized access to data.
- What political consequences did the attack on The Interview imply? In 2014, hackers threatened to attack theaters that showed The Interview. As a result, Sony only showed the movie online and in limited releases.
- Write about cross-site request forgery attacks. Every website tells you that logging out is a crucial step. But what can happen if you don’t do it?
- What is “Anonymous,” and what do they do?
- Is it permissible to hack a system to raise awareness of its vulnerabilities?
- Investigate the origins of the hacking culture.
- How did industrial espionage evolve into hacking?
- Is piracy destroying the music and movie industries?
- Explain the term “cyberwarfare.”
- Contrast different types of hacking.
- Connections between political protests and hacking.
- Is it possible to create an encryption that can’t be hacked?
- The role of hackers in modern warfare.
- Can hacking be ethical?
- Who or what are white hat hackers?
- Discuss what various types of hackers do.
- Is jailbreaking a crime?
- How does hacking a phone differ from hacking a computer?
- Is hacking your personal home devices problematic?
- What is clickjacking?
- Why would hackers target newspapers?
- Examine the consequences society would have to bear if a hacker targeted the state.
- Compare and analyze different hacking collectives.
Topics on Cyber Law & Ethics to Look Into
Virtual life needs rules just like the real one does. The online world brings a different set of values and issues to the table. And, naturally, cyberlife has a legal framework. That’s where researching cyber law and ethics comes into play.
- Is it ethical that governments can always access their citizens’ data? In some countries, online platforms for personal information are standard. From medical exams to debts, everything is available with a click. The system is inarguably convenient. But what about its downsides?
- Is it still morally permissible to use Spotify? Spotify has made listening to music more accessible than ever. However, artists only receive a tiny fraction of the company’s profits. Discuss the implications of this fact.
- Should internet forums require users to display their real names? Online harassment is a widespread problem. Nicknames hide the identities of ordinary users as well as perpetrators. Can the mandatory use of real names change the situation?
- Analyze online gaming behavior from a psychological standpoint. If one wants to play online games, one needs to have a thick skin. The community can be harsh. You can dedicate your paper to exploring these behaviors. Or you might want to ponder what game publishers can do to reduce hate speech.
- What type of restrictions should sellers implement to prevent domain speculation? Some people buy domains hoping that they will sell them later for more money. This practice makes registering a new website trickier.
- Does the internet need regulations to make adult content less visible? Every computer without parental control can access pornographic websites. Most of them don’t require registration. Their contents can be disturbing, and their ads can appear anywhere. What can be done about it?
- What are cyber laws still missing in America? The US has established many laws to regulate internet usage. Select the most significant ones and explain their relevance.
- Why should cyber ethics be different from real-world norms?
- Are there instances in which illegal downloading is justified?
- The rule of law in real life vs. in cyberspace.
- Does the internet need a government?
- What is cyber terrorism, and what makes it dangerous?
- Who is responsible for online misbehavior?
- How binding are netiquettes?
- What did the implementation of the GDPR change?
- Compare and contrast Indian vs. Venezuelan internet regulations.
- What does the CLOUD entail?
- How should law enforcement adapt to online technologies?
- AI applications: ethical limits and possibilities.
- Discuss trending topics in cyber law of the past ten years.
- Should schools teach online etiquette?
- Does internet anonymity bring out the worst in people?
- Is data privacy more important than convenience and centralization?
- Debate whether bitcoins could become the currency of the future.
- How can online consumers protect themselves from fraud?
- Is buying from websites like eBay and Craigslist more ethical than buying from other online marketplaces?
- Present RSF’s Minecraft library and discuss its moral implications.
Cyberbullying Topics for Essays and Papers
On the web, everyone can remain anonymous. With this added comfort, bullying rises to another level. It’s a serious issue that’s getting more and more problematic. Cyber security measures can alleviate the burden. Do you want to address the problem? Have a look at our cyberbullying topics below.
- Cyberbullying prevention in online learning environments. Online classes increase the possibility of cyberbullying. What can teachers do to watch out for their students?
- What makes online emotional abuse particularly difficult to bear? Bullying doesn’t necessarily have to be physical to hurt. Statistics show increased suicide rates among students who were harassed online. Explore the reasons behind this phenomenon.
- How can victims of identity theft reclaim their lives? Identity theft leads not only to mental distress. Thieves also have access to credit card information and other essential assets.
- What are the best methods to stay safe online? When surfing the internet, one always has to be on one’s toes. Avoiding harassment and bullying is a particularly challenging task.
- How can parents monitor their children’s behavior on the web? Children are particularly vulnerable online. They might enter dangerous online relationships with strangers if they feel lonely. They are also more susceptible to scams. What can parents do to protect them?
- Cyberbullying among university students. Online abuse in such websites is very common. Everyone can be a potential target, regardless of age or gender. Discuss whether the structure of social networks helps to spread cyberbullying.
- What societal factors contribute to online bullying? Not everyone who uses the internet becomes an abuser. It’s possible to establish several psychological characteristics of cyberbullies. Explore them in your paper.
- Define how cyberbullying differs from in-person harassment.
- Establish a link between feminism and the fight against cyberstalking.
- The emotional consequences of physical vs. verbal abuse.
- The effects of cyberbullying and academics.
- Short vs. long-term mental health effects of internet bullying.
- What are the most widespread means of cyberbullying?
- Should people who want to play video games online get over the fact that the community is toxic?
- Is defending the freedom of speech more important than preventing the spread of hate speech?
- Reasons and consequences of Amanda Todd’s suicide.
- The dangers of pro-ana/-mia communities for adolescents.
- What are effective strategies to cope with online harassment?
- Would cyber communism decrease bullying?
- How enhanced cyber security measures can help reduce abuse.
- The importance of parental control mechanisms on children’s computers.
- Traditional vs. cyberbullying in children.
- Do image-heavy websites such as Tumblr and Instagram affect one’s mental state similarly to active abuse?
- What kind of people does cyber abuse affect the most, and why?
- Analyze how the stalker uses the internet in Netflix’s series You.
- Catfishing: effects and solutions.
Information Security Topics to Research
Information security’s goal is to protect the transmission and storage of data. On top of that, network security topics are at the forefront of InfoSec research. If you’re looking for inspiration on the subject, check out these ideas.
- What are the mechanics of password protection? Passwords are a simple tool to ensure confidentiality. What do users and developers need to keep in mind when handling passwords?
- What are the safest ways to ensure data integrity? Everybody wants their data to be intact. Accidental or malicious modifications of data can have dire consequences for organizations and individuals. Explore ways to avoid it.
- How can one establish non-repudiation? Non-repudiation proves the validity of your data. It’s essential in legal cases and cyber security.
- How did the advent of these new technologies impact information security? Mobile networks have changed the way we access information. On a smartphone, everything is permanently available at your fingertips. What adverse consequences did these technologies bring?
- How do big corporations ensure that their database environment stays conflict-free? We expect our computers to always run fast and without errors. For institutions such as hospitals, a smooth workflow is vital. Discuss how it can be achieved.
- Describe solid access control methods for organizations. In a company, employees need access to different things. This means that not everyone should have an admin account. How should we control access to information?
- Medical device cyber security. For maximum safety, it’s best to employ several measures. Protection on the hard- and software side is just a part of it. What are some other means of security?
- Write an argumentative essay on why a career in information security doesn’t require a degree.
- Pros and cons of various InfoSec certificates.
- Cybersecurity in cruise ship industry
- The influence of remote work on a businesses’ InfoSec network.
- What should everyone be aware of when it comes to safeguarding private information?
- Select a company and calculate how much budget they should allocate on cyber security.
- What are the dangers of public Wi-Fi networks?
- How secure are cloud services?
- Apple vs. Microsoft: whose systems offer better security?
- Why is it important to remove a USB flash drive safely?
- Is it possible to create an unguessable password?
- Intranet security: best practices.
- Does the use of biometrics increase security?
- Face recognition vs. a simple code: what are the safest locking options for smartphones?
- How do you recover data from a broken hard drive?
- Discuss the functions and risks of cookies and cache files.
- Online privacy regulations in the US and China.
- Physical components of InfoSec.
- Debate security concerns regarding electronic health records.
- What are unified user profiles, and what makes them potentially risky?
👨💻 Cyber Security Thesis Topics
- Analysis of ethical hacking. Analyze ethical hacking, its key features, and types. Research real-world cases of ethical hacking along with the legal and ethical issues surrounding it.
- Redefining privacy in the age of cloud reliance. Since more and more people are relying on cloud services for communication and storing information, concerns about data privacy grow. Examine potential regulations and societal changes required to balance privacy and convenience.
- Privacy concerns across key industries. Discuss the implications for personal privacy in sectors like healthcare, finance, and law enforcement. Dwell on the new methods used to bypass biometric authentication systems, such as facial recognition or fingerprint scanners.
- The human cost of cryptocurrency breaches. Explore the economic and psychological consequences of successful attacks on the crypto market. Showcase the efforts of experts to bolster crypto security.
- Potential impact of law enforcement and tech cooperation on cyberattacks. Propose a scenario for a global collaboration between law enforcement agencies and tech companies to track cybercriminals. Analyze the feasibility, logistical challenges, and potential impact of such collaboration.
- The issue of employing weak protocols for encryption.
- Flexible and adaptive electronics and their role in cybersecurity.
- The use of penetration testing in mitigating cyber threats.
- Analyze emerging attacks in the cybersecurity field.
- Risk assessment in cyber-physical systems.
- The ethical side of popular cybersecurity measures.
- Cybersecurity in educational institutions and its characteristics.
- Study the use of smart wearable sensors for protecting user data and ensuring device integrity.
- The laws and regulations of mobile cybersecurity.
- Cybersecurity challenges in the medical industry: protection strategies.
- Suggest possible solutions to digital payment information theft.
- Inefficient data sharing techniques and their consequences.
💽 Cyber Security Topics for Presentation
- Ethical dilemmas in the digital age. In your presentation, illustrate the potential challenges and ethical considerations associated with cybersecurity. Provide examples of how these technologies can protect against new types of attacks.
- The psychological effects of using the dark web. Show the psychological impact of using the dark web. You can analyze its potential to manipulate, exploit, or offer refuge and support. Find real-life examples to explain how extremist groups and criminal organizations use the dark web to radicalize and recruit vulnerable individuals.
- The role of encryption in protecting information and IoT. Study the fundamental principles of encryption and their role in securing digital information. Discuss how encryption contributes to the security of IoT devices and networks.
- The evolving role of firewalls in cybersecurity. Review the key trends in the evolution of firewall technology and explain how it has adapted to address cyber threats. Highlight the impact of firewalls on cybersecurity for individuals, businesses, and critical infrastructure.
- Measure the cost of cyberattacks across borders. Compare different countries, and industries affected by cyberattacks. Quantify the cost of cybercrime, including stolen funds, business disruption, and downtime.
- The structure of the dark web and its key characteristics.
- Strategies for safe use of public Wi-Fi networks.
- The impact of cybercrime on the economy.
- Popular antivirus programs and their effectiveness in protecting computer systems.
- Trace the development of standards and certifications in the field of cybersecurity.
- Ways of combating fake news and disinformation in cyberspace.
- The effective methods of generating strong passwords.
- Strategies to combat cybercrime in business.
- Cybersecurity professions and their challenges.
- Evaluate the effectiveness of two-factor authentication in account protection.
- Cybersecurity trends: new information protection technologies.
- Principles and types of encryption algorithms in cryptography.
❓ Cyber Security Research Questions
- How can we optimize cybersecurity in schools? Investigate the main factors influencing the effectiveness of cybersecurity in the educational field. Provide actionable tips to protect personal information within the school environment.
- What are the most promising and cost-effective methods to prevent attacks on critical infrastructure? Research innovative methods that prevent attacks on critical infrastructure and ensure its security. Examine the aspects of implementing these innovative methods, including cost and infrastructure compatibility.
- What are the key risks associated with cloud-based platforms in supply chain management? Analyze the risks associated with cloud-based platforms in supply chain management. Then, propose effective security measures for data protection.
- Do legal frameworks adequately address the complexities of state-sponsored cyberattacks? Compare and contrast the legal frameworks surrounding state-sponsored cyberattacks across different countries. Explore the potential for escalation of state-sponsored cyberattacks into armed conflict.
- What are the best practices for secure mobile data exchange on public Wi-Fi? Evaluate the risks associated with public Wi-Fi networks and review the best practices for secure mobile data exchange in these environments. Investigate the role of mobile network operators and device manufacturers in ensuring the security of mobile data exchange.
- How can we ensure security when working with cloud data storage?
- What is the value of continuous user authentication on mobile devices?
- What are the effects of RSA on network security?
- How can we ensure the responsible use of AI in cybersecurity?
- How does using cyberattacks in armed conflicts complicate international norms and legal frameworks?
- What are the benefits of application logging?
- What are the most effective methods for companies to guarantee data security with a remote workforce?
- How can we effectively ensure cybersecurity in the IoT?
- What are the most secure methods of maintaining data integrity?
- What are the best practices for mitigating cyber risks in digital supply chains?
- How can blockchain technologies improve reliability and transparency in cybersecurity?
- What trends and new threats in cyberspace should we expect in the coming years?
💡 Cyber Security Debate Topics
- Face ID: friend or foe? Research the technical security of Face-ID, its strengths and weaknesses. Explain why you consider this technology safe or unsafe, supporting your arguments with statistics and expert opinions.
- How should self-driving cars be regulated? Provide your view on the measures and regulations that should be implemented to ensure the cybersecurity of self-driving cars. Clarify why prioritizing passenger safety and public trust in this emerging technology is essential.
- Unrestricted AI deployment in cybersecurity: benefits and risks. Highlight the potential advantages and disadvantages associated with unrestricted AI deployment in cybersecurity. Can this process speed up threat detection?
- Mandatory reporting of cybersecurity incidents: pros and cons. Provide your opinion on the benefits and drawbacks of compulsory reporting to the public when a company experiences a cybersecurity incident. Support your argument with a real-life example.
- Penalties for cybercriminals: is there room for improvement? Examine the effectiveness of current penalties for cybercriminals. Add your view on how they can be improved, considering the evolving nature of cyber threats.
- Should hackers be helping the FBI?
- What should be done to secure self-driving cars from cyber-attacks?
- Should companies pay ransom to recover stolen data?
- Should international standards be introduced in the field of cyber security?
- Are biometric authentication methods more secure than passwords?
- Should governments use “cyberweapons” as a preventive measure?
- Will synthetic media impact the future of trust and identity in the digital age?
- Should there be restrictions on the use of AI in cybersecurity?
- Is standardized cybersecurity training necessary for all employees?
- Should educational programs include cybersecurity training at all levels?
- Is it ethical for the government to collect information about its citizens?
- Should companies tell the public when they get hacked?
✨ Interesting Topics in Cyber Security
- Security challenges in immersive virtual worlds. Analyze the unique security challenges posed by such environments. Consider technical vulnerabilities and potential social engineering exploits within them.
- Email threats in large companies. Discuss the challenges of identifying and mitigating email-based threats in large organizations. Propose innovative solutions for securing email communication and educating users about email safety.
- Deepfake technology in cyberattacks. Explore the evolving capabilities of deepfake technology and its potential future applications in cyberattacks. Additionally, discuss the challenges of detecting and mitigating deepfakes.
- Strong privacy practices in famous companies. Choose a well-known company that has successfully implemented strong privacy practices. Analyze its methods and explain how they can come in handy for other organizations.
- Private sector partnerships in global cybersecurity. Investigate the role of private sector partnerships in international cybersecurity efforts. Take into account their benefits and potential conflicts of interest.
- Email attacks and their characteristics.
- Study the issue of cybersecurity workforce shortage.
- AI-generated images and their role in the evolution of cyber threats.
- The importance of data privacy discipline.
- Ways to stay safe during online video calls and conferencing.
- The use of synthetic data in creating fake identities.
- Cybersecurity risks of remote working.
- Ways to protect privacy online as a business.
- The rise of ransomware and possible solutions.
- International cooperation in cyber security and its effectiveness.
- Evaluate the weaknesses of cloud-based services.
- The psychological aspects of cyberattacks.
💾 Operational Security Research Paper Topics & Prompts
Operational security is a vital dimension in the field of cybersecurity. You may explore the following topics in your writing to get a better grasp of its specifics:
- Sensitive data management. Research the types of sensitive data to understand the development of effective security strategies for an organization.
- Potential threat detection. Examine the range of threats to data integrity and their sources. What role do they play in the current cybersecurity landscape?
- Vulnerability assessment. Explore internal and external data vulnerabilities to understand how organizational data may get under attack.
- Risk level and its management. How can an organization detect and prioritize risks to allocate defensive resources wisely?
- Mitigation strategy development. In this essay, describe how cyber threat mitigation strategies are developed. What helps keep business data intact and minimize risks?
📡 Mobile Cybersecurity Research Topics
Exploring mobile cybersecurity can lead to a wealth of intriguing research topics:
- The significance of continuous user authentication on mobile gadgets
- Compare the efficacy of different mobile security approaches
- Ways of detecting mobile phone hacking
- The threats in using portable devices to access banking services
- Cybersecurity and mobile applications
- The vulnerabilities in wireless mobile data exchange
- The rise of mobile malware
- Trace the evolution of Android malware
- How to know you’ve been hacked on mobile
- The impact of mobile gadgets on cybersecurity
🤔 How to Choose a Cybersecurity Research Topic?
Choosing a relevant, engaging, and manageable topic is vital for any assignment. Here are some pro tips to guide you in selecting a topic for a cybersecurity-related task:
- Brainstorm. You can quickly map out the most suitable topic options by brainstorming the latest cybersecurity research. Choose an aspect that interests you the most and make a quick list of potentially interesting subtopics. Scan relevant blogs, forums, and social media to see what currently interests people in these areas.
- Research. Now that you have several workable topic suggestions, it’s time to get down to in-depth research. You need to expand your knowledge on the subject by reviewing academic sources and industry reports from recognized authors.
- Scope. After extensive research, you will collect plenty of evidence. At this next stage, you need to narrow it all down. Refine your topic by balancing the breadth and depth of analysis. Double-check that your selected issue has sufficient coverage in academic sources to give you enough supportive material.
- Be flexible. Feel free to adjust the topic as you write. After reading several sources and diving deeper into research, you can find a more interesting angle to focus on.
These strategies are suitable for all kinds of cybersecurity research. They will help you land on the winning topic without wasting time.
✍️ How to Write a Cybersecurity Research Paper?
Even if cybersecurity research seems complicated, a structured approach can make the process simple and enjoyable. Follow these steps to make your cybersecurity-related task more manageable:
- Grasp every aspect of the prompt. Read the task attentively and make notes about the topic and required structure. This way, you will avoid confusion or going off-topic.
- Choose the topic wisely. It’s important to spot an original topic relevant to the present-day cybersecurity industry, suitable in scope for your task type, and interesting to you personally.
- Research the chosen area. Next, you should compile a solid dataset from various academic sources, such as journals and industry reports. Use Google Scholar and IEEE Explore to find reliable and fresh evidence in this area to raise the authority of your voice.
- Develop a winning thesis statement. The collected evidence will help you write an impactful and clear thesis statement. It will condense your main idea and guide the readers through the essay.
- Outline the paper. By writing a detailed plan, you create a roadmap for writing. It’ll ensure your content’s logical flow and comprehensive content coverage.
- Draft the paper with clarity in mind. The next stage is writing your first draft. Pay attention to detail and a clear flow. You would also need to compose a topic sentence for every paragraph and link it to the thesis statement. Finally, ensure that all material in each paragraph aligns with your topic.
- Mind the format. In-text referencing, the list of used sources in the bibliography, and your paper’s overall format should align with the selected referencing style, such as APA, MLA, or Harvard. Check your educational institution’s requirements to make sure you do everything correctly.
These steps are a sure path to a winning essay that will get you a high grade.
Thanks for reading through our article. If you found it helpful, consider sharing it with your friends. We wish you good luck with your project!
Further reading:
- 220 Best Science and Technology Essay Topics to Write About
- 204 Research Topics on Technology & Computer Science
- A List of 580 Interesting Research Topics [2026 Edition]
- A List of 179 Problem Solution Essay Topics & Questions
- 193 Interesting Proposal Essay Topics and Ideas
- 226 Research Topics on Criminal Justice & Criminology
🔍 References
- What Is Cybersecurity?: Cisco
- Federal Bureau of Investigation Internet Crime Report 2023: Internet Crime Complaint Center (IC3)
- Cybersecurity: National Institute of Standards and Technology
- What Is Information Security?: CSO Online
- Articles on Cyber Ethics: The Conversation
- What Is Cybercrime?: Kaspersky
- Types of Cybercrime and How to Protect Yourself Against Them: Security Traits
- Hacking: Computing: Encyclopedia Britannica
- Hacking News: Science Daily
- Cyberbullying and Cybersecurity: How Are They Connected?: AT&T
- Cyberbullying: What Is It and How to Stop It: UNICEF
- Current Awareness: Cyberlaw Decoded: Florida State University
![Student Exchange Program (Flex) Essay Topics [2026]](https://custom-writing.org/blog/wp-content/uploads/2021/01/student-exchange-program-284x153.jpg)







![500 Sociology Questions and Topics [Examples & Tips]](https://custom-writing.org/blog/wp-content/uploads/2021/01/Sociology-Questions-284x153.jpg)

